
StaFi Protocol rFIS Bug Bounty
Add to Watchlist
Added to Watchlist
Reward pool
Unknown
equal in FIS
Expected profit
from ~$10
equal in FIS
Max participants
∞
No limit
DropsEarn score
Neutral
Normal, Low Risks
Event details
Overview
It is the mission of StaFi to unleash the liquidity of all Staked assets. The team has worked tirelessly towards this mission since Day One, pulling all-nighters one after another. Team are finally ready to announce a substantial progress that team have made: the development of the main functions of rFIS have been completed. rFIS product is ready to enter Open Beta: https://test-apps.stafi.io/?rpc=wss%3A%2F%2Fstafi-seiya.stafi.io#/accounts
It should be noted that it is the open beta version of rFIS that team are launching. The main purpose is to test the process, function, and security vulnerabilities, and so there is no UI for terminals. The team, however, is currently developing a more user-friendly UI, which will be available when rFIS is officially launched.
Test Incentives
1. Test document
https://docs.stafi.io/rproduct/rfis-solution/rfis-testing-guide#stakers
This test encompasses two parts, one is user test incentives, and the other is validator test incentives. Only validators need to test Onboard and Offboard operations, and users don’t. Moreover, validators also need to run Seiya testnet nodes first.
2. Duration
- Testing time starts: 21:00 on December 3, 2020 (UTC+8)
- Testing time ends: 21:00 on December 17, 2020 (UTC+8)
- Starting block height: 751876
- End block height: 953476
3. User testing tasks & incentives
- LiquidityBond: Exchange FIS for rFIS
- Transfer: rFIS transfer
- LiquidityUnbond: Redeem FIS through rFIS, and execute
- liquidityWithdrawUnbond operation after 56 Eras.
- Liquidity_withdraw_unbond: Withdraw the redeemed FIS, please confirm whether the exchange rate calculation is correct after withdrawal.
Notes
- In the Seiya testnet, one Era=1 hour.
- As for the exchange rate calculation, please refer to: https://medium.com/stafi/stafi-officially-announces-rfis-liquidity-solution-for-its-native-token-fis-31f2e6b1e4ff
- When withdrawing the redeemed FIS, it is necessary to calculate whether the amount of FIS obtained is correct by the current exchange rate. Please note that a 10% handling fee will be deducted from the reward.
Incentives
During the test period, the first 100 participants who complete all of the above tasks will receive 10 FIS (FIS of mainnet) award. Please carefully memorize the account and key, for the incentive will be sent to this account.
When all tasks are completed, please forward the relevant tweet from StaFi’s Twitter account and attach the screenshot of the successful operation of LiquidityBond and LiquidityWithdrawUnbond operations). Moreover, please @ three of your friends and the FIS address to receive the reward.
4. Validator tasks and incentives
Tasks:
- Run Seiya testnet node during the testing period, and register as a validator while keeping the validator node stable: https://docs.stafi.io/network-1/seiya-public-testnet
- Complete the following tasks in order:
Onboard: Register as a validator
Offboard: cancel validating
Onboard: Register as a validator
LiquidityBond: Exchange FIS for RFIS
Transfer: rFIS transfer
LiquidityUnbond: Redeem FIS through rFIS, and executeliquidityWithdrawUnbond operation after 56 eras.
Liquidity_withdraw_unbond: Withdraw the redeemed FIS, please confirm whether the exchange rate calculation is correct after withdrawal.
Note
- You need to run the Seiya testnet node first before participating in the validator test.
- When performing Onboard operations, you need to use the Controller account
- In the Seiya testnet, one Era = 1 hour.
- As for the exchange rate, please refer to: https://medium.com/stafi/stafi-officially-announces-rfis-liquidity-solution-for-its-native-token-fis-31f2e6b1e4ff
Incentives
The first 40 validators who complete all the above tasks during the test period will receive 50 FIS (FIS of mainnet) as reward. Please be sure to memorize the account and keys, for the test incentive will be sent to this account.
Before the test, you need to join the StaFi validator test group: https://t.me/stafi_testnet. When you complete all tasks, please send the screenshot of the LiquidityBond and LiquidityWithdrawUnbond operations and the FIS address used to receive the reward.
For all malfunctions or bugs discovered during the test, please feel free to report to through the same channel of bug submission(see below).
Code vulnerability testing incentives
1. Test content
2. Criteria
- Critical: Abnormal function, ineffective function, or security breach, etc.;
- Moderate: Defects that do not affect the function, non-security issues, such as the room for optimization, performance improvement, etc.;
- Low: Unimportant issues, some minor issues that can be modified during updates, such as modifying text or notes.
Outside the scope of the bounty program
- Repeated reports on security issues, including security issues that have been confirmed by the StaFi team;
- Theoretical security issues without pragmatic application scenarios, or issues that require complex user-interactions.
3. Rules
- It must be a newly discovered bug(s) that has/have not been reported before
- The bug(s) found must be related to security issues in StaFi GitHub page code, but not other third-party code;
- Have not written any codes of StaFi around the bug(s), and have not participated in any process that generated the bug(s) of StaFi in other ways;
- Public disclosure will make you lose your bounty;
- The StaFi team reserves the right to make the final decision on eligibility for the event and all rewards.
4. Bounty rules
The bounty will be issued in the form of FIS, and the amount will depend on the severity of the bugs found.
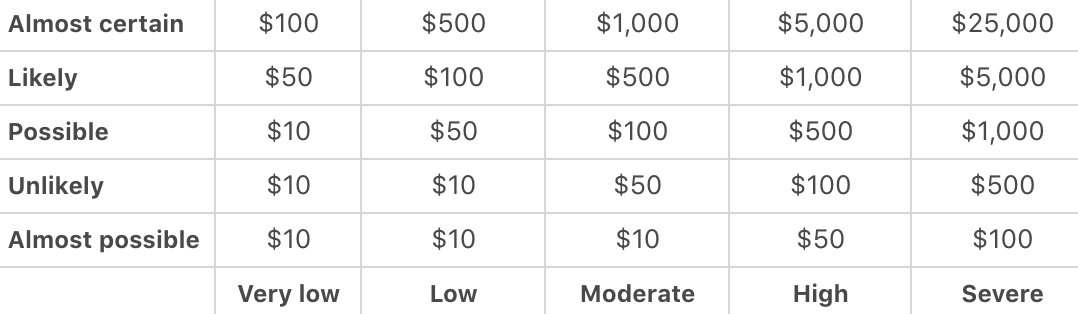
In addition to severity, the bounty amount will be determined (but not limited to) by other factors including:
- The accuracy and details of the bug description;
- The quality of reproducibility, such as test code, scripts, and detailed instructions.
5. Submission Method
When you find bug(s), please send a report to: [email protected]. Please attach your name, email, company name (optional), description of the bug(s), your opinion on what is the potential impact of that bug on StaFi rBridge, and how you discovered that bug.
Socials
- Website: www.stafi.io
- Twitter: @Stafi_Protocol
- Telegram Chat: https://t.me/stafi_protocol
- Telegram Announcements: https://t.me/stafi_ann
- Discord: https://discord.com/invite/jB77etn
- Forum: https://commonwealth.im/stafi
About
The team has completed almost all code work of rFIS but has not yet conducted a security audit. All community members and validators are welcome to the test, and team will give generous rewards for the detection of security, code, and functional vulnerabilities.
Activity Type
Date
3 Dec 2020 18:00(UTC+3) - 17 Dec 2020 18:00(UTC+3)
Registration
Closed
When Reward:
None
Event Status
Links

